New Document Public Wi-Fi networks – you find them at airports, coffee shops, and even speedy meal-eating places. Public networks do not have to be wireless. Hotel networks are frequently stressed. However, they may be shared, and identical precautions apply. You by no means know who else is at the network capturing your traffic. Are public networks secure? What can you do to shield yourself?

The first one is antique-school and low-tech (or even no-tech). Someone who wants to scouse borrows your passwords or see what you’re as much as can sincerely look over your shoulder (it’s miles called shoulder-browsing). There is a more boosted version, though. It involves a small video digicam strategically located to record what others are doing – from time to time, from a distance of numerous meters. Watching the display and gambling returned video of the keystrokes while getting into passwords may be a powerful assault. In a crowded vicinity, and with the right gadget, this is simpler than you may assume.
The 2D one is, without a doubt, shooting the site visitors that you are broadcasting through the air (it’s why it is referred to as wifi, you already know) and reading it later for passwords and many others. Many public networks are open (all of the site visitors are in “plaintext” and maybe study) or use shared passwords (in case you all have an equal password, it is extra or less similar to an open network). Assume any password given to you by someone else is not comfy because you don’t understand who else may additionally comprehend it.
The third one is a touch more difficult, but not plenty. Anyone can faux to be unfastened wifi gets entry to factor. It simply takes a touch configuration on a PC to install a network others can connect to. The attacker calls it “Free Public wifi” and then connects any victims who fall for the trick to an actual public community. The victim surfs, thankfully, but the attacker is recording the entirety.
Avoid doing touchy work while in a public community. Do you need to test your stocks or bank account from the lodge or espresso keep? Only do this while it’s far more sincerely important. Know what you are connected to. Make sure you realize the call (additionally referred to as the SSID) of the community you want to apply to. Beware if you see a replica or comparable name. Avoid unknown networks. Your PC should also be configured to hook up with the “get entry to factors” most effective (also known as infrastructure mode). Do not let your PC connect simultaneously to different computer systems (an ad hoc mode).
Learn about HTTPS. In the deal with a bar of the browser, coping starts offevolved with either HTTP:// or HTTPS://. The “s” stands for cozy. In this mode, all site visitors to and out of your computer are encrypted and can not be studied by using everybody else – even supposing they report it and examine it later. Any sensitive statistics need ONLY to be sent over an HTTPS connection. A word of caution, though – if you are tricked into making an HTTPS connection to an attacker, they’ll be capable of examining what you ship.
You have to be SURE who is on the opposite gives up the HTTPS connection. If you get hold of an error about a “certificate” on a public network, DO NOT ignore it. You can be approximate to emerge as a sufferer. Checking email? Remember that even though you could check in on your account using HTTPS, the mail is generally despatched over HTTP, in cleartext. The exception is Gmail, which defaults to HTTPS for everything. It is the maximum comfy email service to be used in public locations. If the ultimate recommendations sound a chunk complex, they may be. The right news is that you could bypass them if you need to and go to tip range five.

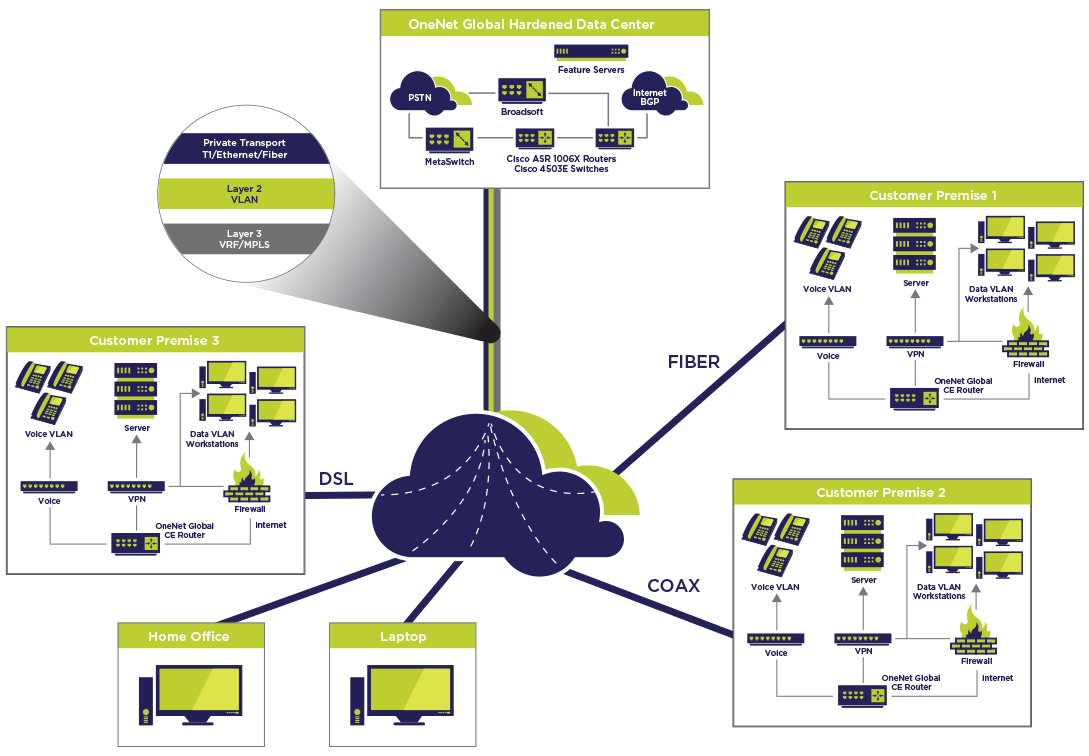
Use a VPN or a comfortable connection service. Use a VPN or a comfy connection if you need to be safe. With a VPN, your PC does not join the net at once. Instead, it makes a cozy (encrypted) connection to some different laptop, which connects to the internet from a non-public network. Examples are LogMeIn and GoToMyPC. There are many others. There are free versions and paid versions with greater superior features. You can install these on a domestic or workplace PC.
However, you must configure your home or workplace router to make all its paintings. Cozy offerings depict the same manner, except that their servers establish real connections to the internet. They are commonly simpler to configure. Examples are HotSpot VPN, Witopia, and Hotspot Shield. Again, a few are loose, and some are paid subscription services.
You see, computing from a public location may be secure. The first and 2d recommendations are excellent, not unusual-sense approaches to avoid needless risks. However, the 2d and 0.33 pointers are a chunk “nerdy,” they correct safety practices. Tip range five is the best and almost bullet-proof, as long as you comply with the tip number. You don’t need to spend money, but spending a bit may also get you some introduced velocity, comfort, and functions. Use your head (to dam the keyboard’s view when typing passwords, this is), pay interest, and be secure.



